Welcome, everybody. I'm Rob Kraczek. I'm on the field strategy team. Marcus.
Yeah, I'm Marcus Weiss-Ehlers. I'm on the Identity Manager team, work with Matthias Bauer.
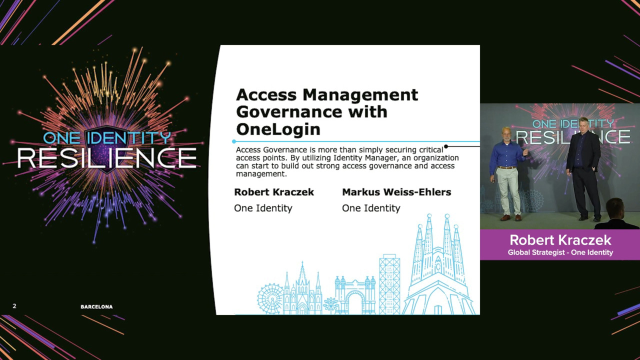
So today we're going to talk about access management governance with OneLogin, and Marcus, actually is, I don't know, I think some of you saw the keynote yesterday, where I just showed a quick, little snippet of that integration. Marcus, actually, has developed some great demo videos that we're going to show you on that integration going much further than what I showed in my brief 3 minutes.
So we're going to do an overview of the connector at a high level. We laid out some customer benefits, and they're kind of general, because we wanted to make them as broad as possible just to cover the basics. I mean, I'm sure we have a good mix of partners and customers in the room. As we step through some of these samples, you're going to find that the gears are going to turn on what you can do with these integrations.
And I'm actually excited to see over the next fiscal year, as we start rolling out these integrations between OneLogin and Identity Manager, in particular, what you come up with in the field. And support i probably not that excited, but we have a number of different features and functions coming out with the new connector, and there's also a lot of capabilities that you can extend beyond what's going to be out of the box to create a really great solution.
So if we talk about what the Identity Manager use case or what are the Identity Manager connector is going to be able to do, obviously, we have to look at the products themselves. How many of you are Identity Manager implementers or users? Right, just about all of you, so that's a comprehensive IJA solution. So you have lifecycle management, governance, X basic joiner-mover lever functions, a huge library of connectors. It just basically does everything you need for IJA.
And then if you look at OneLogin, it's a great access management portal with excellent capabilities in the launchpad and risk assessment, and the vigilance AI, the ability for you to map attributes between Identity Manager and OneLogin. There's a lot of capabilities behind the scenes that you can leverage in that solution to combine the two to create a better whole.
So if we look at OneLogin and access management governance, we're actually taking the best, both of these tools, and we're combining them into a really versatile environment that you can leverage for a number of use cases. And I think Darren mentioned 1 plus 1 equals 3, and I think this is the case with these two products.
Because if you look at access management by itself, those products are not really aware of all the intricacies of an application behind the scenes. They're not aware of entitlements and access rights and the need to do access reviews and do cyclical governments of the entitlements or the applications. And so by combining these two solutions, we can create a big picture view of, at least from an IJA perspective, of the life cycle of that access entitlement and how they're getting access to it through the OneLogin portal.
So let's talk about a couple of customer benefits. Actually, we have three. And again, these are fairly broad. We wanted to try and cover as much as we could with these three, but obviously, there's more that you can apply.
Least privilege or zero trust. So again, that's a paradigm or a concept on how you can establish some controls around high-risk, high-priority resources. And so we're going to show step-up authentication using the OneLogin capabilities within Identity Manager.
Entitlement data on access rights. Being notified of when rights have been assigned or have been used over a certain period of time. That is something that we can consume from OneLogin, and then we can take action, which is an important part of marrying an access management portal to an IJA solution, and that leads into access reviews.
So performing regular attestations, make sure that things are visible to administrators so that when things either happen in real time or whether it's a cyclical thing, where you're running a regular review, you can add or remove applications based on this integration from the portal on regular access reviews or auto-generated entitlement reviews.
And so I don't know if anybody has any other use cases they can think of between these integrations, because it's a very important thing. You can see other vendors in the access management space trying to introduce governance into their programs, either self-development or through partnerships, and I don't think there's an access management vendor out there today that doesn't have some sort of at lease market architecture around governance and the integration of the two platforms.
So let's talk about functions. I don't know if you wanted to get into it?
Yeah, I can get that one. So what we're showing here, these are the functions that the one locking module or the one locking connector currently provides out of the box. So what we're doing, the people that attended the United Budapest might find some similarities between the privileged access governance module and this module here.
So we synchronize information from OneLogin to Identity Manager, we're doing the user correlation to the identities, of course. So let's say we have a slide later on to that, so where do we start first when you integrate those two products? You can start on the Identity Manager side or the OneLogin
Let's assume you have already OneLogin and you bring Identity Manager in, so you already have your users, that [INAUDIBLE] identities, how to get them into Identity Manager. So this is covered out of the box, so we read in the user, so you can create the identities in the Identity Manager, and then you can go to start.
The addition, if you do have Active Directory base setup in OneLogin, we do correlate the Active Directory users as well. So if Identity Manager knows the Active Directory users, we do the linking between the OneLogin user and the Active Directory user and the Identity in Identity Manager. So this is something that's coming out of the box.
Of course, we do provisioning of users and roles in OneLogin. I will talk later on, that there's plans, more things to do, so we are showing that in one of the demonstrations as well. And again, of course, at this stage of recertification of OneLogin users, role memberships or application access, and this, again, one thing we're going to show in the demonstration video.
Of course-- the fourth time I said, of course, but again, user access request. So you can go to the shop, you can request the access either to the OneLogin application dashboard, or to a specific application. You can work all through the normal approval policies. You can do recommendations in the approval workflow. We're going to show that as well. And if you do have critical access, risky access, we can force you to do MFA by step-up authentication in the IT shop using OneLogin.
So these are the core functions that are in the product right now, and so we're going to demonstrate some of the functions now.
And then we're going to talk about some of the future things after this. So we'll get into it and solicit feedback from you guys after the demonstrations, then we talk about futures. So if you have any suggestions or any use cases you've seen in the field, we'd love to hear them.
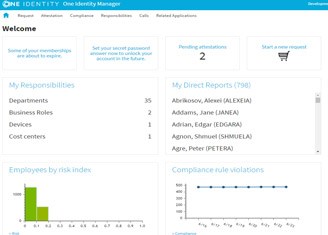
OK. So before we start the demo video, the demo videos are using two personas, in general. So there is a user, which is called or she is called Millie Arbuckle. I made the names up. So she's requesting something. In the first video, she requests access to OneLogin, and she gets access to a famous resilience application. Then we see her manager approving that, looking at the request, taking a look at the recommendations.
And then it's going to approve the request, we can see in the first demonstration, that she gets access into the OneLogin dashboard portal. So we're be using these two personas in all of the four videos I'm going to show, so we have four use cases, four videos, two personas, just keep that in mind. I hope the videos are not so fast. I'm trying to talk over the videos.
If something is unclear, I would propose after one video, then we have two Q&A's, a short Q&A, was something unclear for this use case, and then we go on with the next use case. So if you can please start the video.
There you go.
So now here, Millie Arbukle looks to the OneLogin, Identity Manager portal, and now, searches for the OneLogin user, and she wants to request that access. She goes to the card, and you can see here that she automatically gets a resilience application as well. So when she logs in, she should see the resilience application as well.
Now, our manager is going into the portal here and is checking the pending request. Of course, he could get a notification just for making the use case simple here. Then he goes checking the recommendations for both. What he can see here, of course, one red item. This is a peer group analysis. Only 88% of a peer group using that, and the other one is from the wrong functional area because she's not in the marketing department.
And so I approve it anywhere. Come on. It's just a recommendation. It's not-- have to. We could have built the use case as well so that if a recommendation fails, the request is automatically denied, but just for the demonstration purposes to show all the capabilities that's why I've chosen this use case. The access is needed. I approve it anywhere, anyway. And now, this is closed.
So sometimes later, she gets notified, hey, you're good to go. Just log into the OneLogin portal. She logs in, provides a password, and she should see the resilience application. Magic. So this is the end of the first use case. Awesome. I heard awesome. Say it again, awesome. Right.
So this is one way of integrating. So Identity Manager now is the master in that case. We create the identities or the users in OneLogin. As I told you before, I'm not showing that, it's just because it's too technical, I would say. We're not showing the other way around, so OneLogin users coming into Identity Manager like you see in the next use case.
So Millie works a little bit later. She requests some access. Now, she requests some super risky access. Now, again, the manager has to approve, and therefore, we're using an MFA-based, step-up authentication to approve that request, and this is the thing that we show in the next video. So can you show the second?
Yeah.
So he looked at the use case here at the request. You can see here that the risk is high, the last one. The other one you know already, and this was never approved before. There was a null approval. The reason there it states I need this for some firefighting. So even if the recommendation says, no, I shouldn't approve this, I'm going to do that, but I have to provide my step-up authentication using OneLogin.
And so I'm getting a notification on my iPhone and saying, yay, approval. I am accepting that. And then the approval process that Identity Manager moves on. So I am able to provide, for example, limited time that the entitlement is valid-- you can see here that develop until is set-- I'm providing a reason, and I'm improving that.
Yeah, short use case, isn't it?
Yeah.
I think we have a lot of time for questions, aren't we?
Well, you filmed them in 2 times speed.
Yeah. That's why I thought you had my own stop, play, mute on. OK, so this was a short second use case. I promise you the two other ones are a little bit longer. So I didn't want it to bother you because it's, again, shopping approval. Just a step-up authentication.
So next thing is, we do have an unused application access. So Millie, why am I not shown here, oh, you can see this here on the screenshot. She requested an Office 365 app. On this video, it's still requested, so she gets this approved sometime later. The system detects, hey, Millie didn't use Office 365.
So we get a notification, and then she gets an email, hey, you didn't use it. Are you sure? Why are we showing this one? The user can object, so an application access. Anonymous applications access should be removed. Now, you can say, OK, if it's unused, it's unused, throw it away. But sometimes there are reasons to not remove the access.
So we build here in the approval process so that the user can object to the removal. So you can say, hey, I still did it because I didn't have the time to look at it, but I'm still needing it or whatever. So she's going to get the notification here, and then we're working through the process of how this is going to come up then.
You can start the search, will you please? So you see here he gets an email, and in that email, you see that you do have one use, OneLogin application access. And then the information she can see in the email, it's Office 365. She has never used it. Interesting. So she decided to go in and say, OK, I object in that and still need this access for whatever reason.
Think of someone, any reason. She goes into the portal again, goes to the recertification and can see here, we can take a look at the same details, so it never used in the last 90 days, never used at all. And she's going to approve this one because I still need access. Of course, I still need access. I don't want to lose anything. Normally, user act like that. So OK, I still need Office.
So next thing was coming in the workflow, her manager had to approve as well. And now, we show you another feature. Can you stop it? OK, so this is using Starling Cloud Systems, so we're providing using Starling Cloud System, I'm going to send the teams card. And here, my manager is going to opt to deny this request directly in the adaptive card in Teams.
And now, just for demonstration purposes, he clicks on the Show button to show you that there's also, a deep link integration into the portal. So if you may want to look up further information, he can look at that. So OK, yeah, right. So he's going to submit the denial here in the Teams application, and it will be executed then in Identity Manager.
So sometime later, and this is the point in time where I should have paused, Millie is checking her attestation history. What about my objected removal? And she can see here that the manager has said, she doesn't need Office, that's on top here, and that the access has been removed automatically by the system.
Are they really sure to move my Office? So she's going in until one login portal and she checks, just to prove the point here, and Office should be gone.
Third video. I told you we should have done 10. OK, third video. What's left now? We've showed you MFA integration. We have showed you Identity Manager can create users and entitlements using the request. We've showed you that you can notify about changes or unused entitlements, unused application right outside of the box starting recertification, showing or giving recommendations if I should approve that or not.
So what's left now is, I do have a policy, this is the last use case. I do have an application that is not used at all. So what should I do? I'm not going to go and OK, remove all the excess. It's not used, fine.
So what I'm going to do, my manager is getting a notification from the policy, hey, we do have a policy that applications that have never been used in the last 90 days. We're going to remove from the portal for security reasons. You never know. Somebody can sneak in, whatever, or save money.
You made the point saving money if an application is not used. So if you start the use case, the fourth video, please, OK, so here you get a notification. If you look at the exceptional approval information, it states I should start the recertification process to ensure that nobody really doesn't need the application.
So this is what I'm going to do now, or the manager, it's going to the attestation policies, and it's going to do one lock and application access policy. And just to show you what is available there, so this is the normal attestation view, you know all. It has a disabled schedule, so I'm going to do this behavior driven because nobody has used it.
And now, I'm selecting one of the available filter conditions, and I do know that I should select here the Adobe Creative Cloud, because this is the policy that has informed me, hey, Adobe Creative Cloud is not use at all. So I'm going to take a look, how many users accessing this application. In this case here, it's 12 users accessing this one.
And now, I'm starting the campaign. You see this video is slow, all right. So I'm starting the adaptation campaign. into I have here my 12 users. I'm going to select all of them, and start the campaign. Somebody has to mention I could have clicked the other button Start at the stations for all, but anyway.
So now, some time goes by. Everybody is going to approve or deny, and now, I'm looking at the state of my attestation campaign. I can see here, OK, 100% it's finished. Everybody has-- oh there's still some users needed this application, 5 to 7.
So I'm taking a deeper look at the cases, as the decisions, show there are several approved ones or denied ones. I can drill down, take a look at the workflow, why did they need this for whatever reason. And then I can decide, hey, what I'm going to do now, I'm going to remove the application or not.
So I'm not removing the application, of course, because it's still needed. What I'm going to do now is, I'm going to do an Approve and Exception for this policy to say, hey, it's OK for now. And the next time the usage is considered, we can do this all over again.
And then again, for example, the same five users are saying, hey, I'm still using it, but they're not using it, I'm going to say, OK, regardless what you are saying, they're moving the application at all. So that's about the demonstration use cases. So can you show the slides, not the video? Yeah.
There you go.
Thank you, sir. Do you?
Yeah. So what we just saw was Identity Manager to OneLogin, but you could, obviously, tie OneLogin back to Identity Manager and provision to external systems that way. So you can start from both directions to create this integration. I'm curious, how many OneLogin customers are in the room? One.
There you go. Represent. Give him a big applaud. So the point is is that with this integration, you can start from one direction or another. Obviously, the rest of you are IJA customers, so you can just start from that direction, or if you're consultants and you have potential clients that want to use the OneLogin portal, we're going to have this out of the box. Actually, we have existing version now.
So that's a very powerful message, particularly, when you're looking at creating something that's going to go beyond us-- I hate to call IJA simple because it's not simple. But when you're going to go beyond the IJA pillar and start expanding into access management and even PAM and so forth, you can utilize this capability.
Should I take this one?
You take those.
I'll take those. So some of you may have missed the current release. We do not auto publish the OneLogin rolls to the T shop. So this will happen with the next version out of the box. It's just time constrained as we build the integration. So this will be coming up, but you, obviously, can put the roles or so the applications and the roles that control the applications in OneLogin. You can put them into the shop yourselves, as I did.
OK, so we will add ownership processes. So currently, what we don't have is an ownership process for the applications that we read from OneLogin. And this has something to do, we need more APIs. So as we have mentioned before, in some other presentations, on our journey to integrate those products and for some of these integrations, the APIs have to be enhanced, and we are currently in the process in enhancing the APIs on the back, so we can do a tighter integration of these two products.
As well as company policies, out of the box, we have seen some company policies in the demonstration. So I think some of these company policies are planned for the solution accelerator. I think Ted mentioned this in his presentation. So the thing I have shown you today, probably will be available as a solution accelerator and will be integrated into the next, hopefully, service pack of 9.1.
So you have the option to do everything I've done today, just right off the box by applying either one of these. And of course, more reports and dashboards. And as Hannah has pointed out, the dashboard integration into the web portal is going on, so we provide dashboard then as well for this integration and these use cases, or behavior-driven governance use cases, not used for 90 days. Or for my example, I have given an exception for the company policy.
So how many exceptions have been given, but the access is still not used, for example, one thing you can think of. So there will be more coming, and we pointed out about the whole conference this year, so this is a way to go forward. We're going to integrate these tools, we're going to provide the unified platform, and there will be more coming.
I think we're about done.
I think. No one?
You answered all their questions.
Yeah. OK, so then we're finished?
Yeah.
Yeah.
Thank you.
Thank you.
 25:34
25:34